Worry-free Pentesting: Continuous Oversight In Offensive Security Testing
In your cybersecurity practice, do you ever worry that you’ve left your back door open and an intruder might sneak inside? If you answered yes, you’re not alone. The experience can be a common one. This is especially true for security leaders of large organizations with multiple layers of tech and cross-team collaboration. At Synack, […]

In your cybersecurity practice, do you ever worry that you’ve left your back door open and an intruder might sneak inside? If you answered yes, you’re not alone. The experience can be a common one. This is especially true for security leaders of large organizations with multiple layers of tech and cross-team collaboration.
At Synack, the better way to pentest is one that’s always on, can scale to test for urgent vulnerabilities or compliance needs. It also provides transparent, thorough reporting and coverage insight.
Know What’s Being Tested, Where It’s Happening and How Often It’s Occurring
With Synack365, our Premier Security Testing Platform, you can find relief in the fact that we’re always checking for unlocked doors. To provide better testing oversight, we maintain reports that list all web assets being tested, which our customers have praised. Customer feedback indicated that adding continuous oversight into host assets would also help to know which host or web assets are being tested, and when and where they’re being tested. It also shows how much testing has occurred.
Synack’s expanded Coverage Analytics tells you all that and more for host assets. This is in addition to previous coverage details on web applications and API endpoints, all found within the Synack platform. With Coverage Analytics, Synack customers are able to identify which web or host assets have been tested and the nature of the testing performed. This is helpful for auditing purposes and provides proof of testing activity, not just that an asset is in scope. Additionally, Coverage Analytics gives customers an understanding of areas that haven’t been tested as heavily for vulnerabilities and can provide internal red team leaders with direction for supplemental testing and prioritization.
Unmatched Oversight of Coverage
Other forms of security testing are unable to provide the details and information Synack Coverage Analytics does. Bug bounty testing typically goes through the untraceable public internet or via tagged headers, which require security researcher cooperation. The number of researchers and hours that they are testing are not easily trackable via these methods, if at all. Traditional penetration testing doesn’t have direct measurement capabilities. Our LaunchPoint infrastructure stands between the Synack Red Team, our community of 1,500 security researchers, and customer assets, so customers have better visibility of the measurable traffic during a test. More and more frequently, we hear that customers are required to provide this kind of information to their auditors in financial services and other industries.
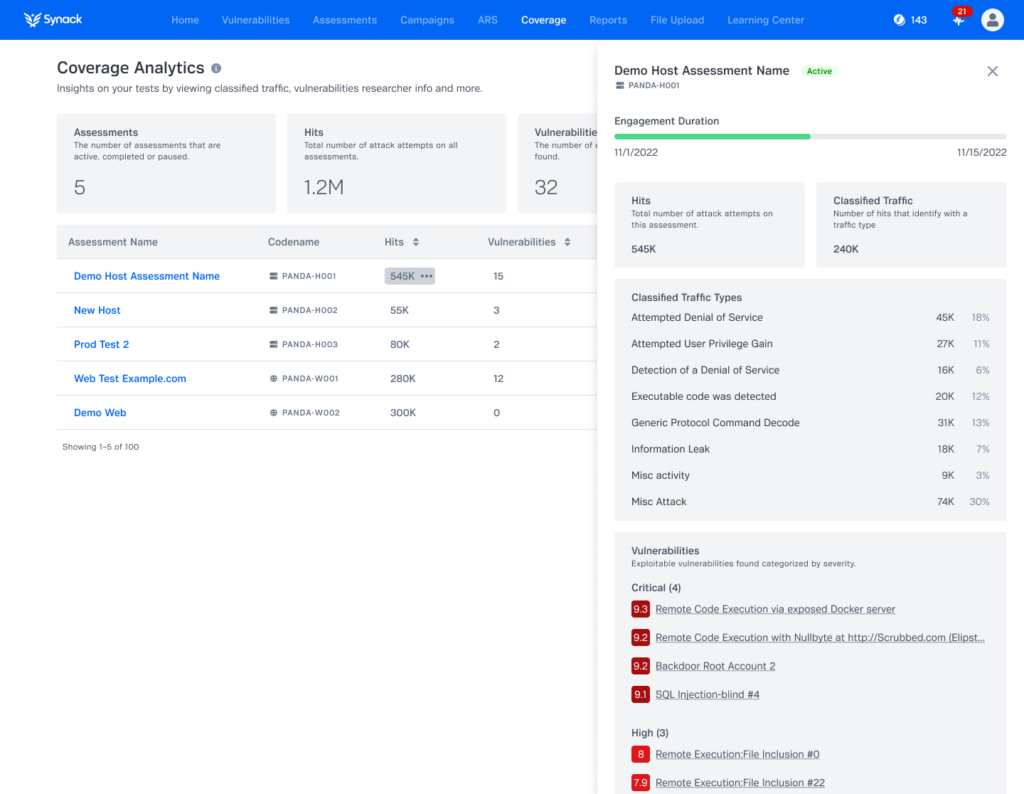
A look at the Classified Traffic & Vulnerabilities view in Synack’s Coverage Analytics. Sample data has been used for illustration purposes.
Benefits of Coverage Analytics
- Know what’s being tested within your web and host assets: where, when and how much
- View the traffic generated by the Synack Red Team during pentesting
- Take next steps with confidence; identify where you may need supplemental testing and how to prioritize such testing
Starting today, security leaders can reduce their teams’ fears of pentesting in the dark by knowing what’s being tested, where and how much at any time across both web and host assets. Coverage Analytics makes sharing findings with executive leaders, board members or auditors simple and painless.
Current Synack customers can log in to the Synack Platform to explore Coverage Analytics today. If you have questions or are interested in learning more about Coverage Analytics, part of Synack’s Better Way to Pentest, don’t hesitate to contact us today!