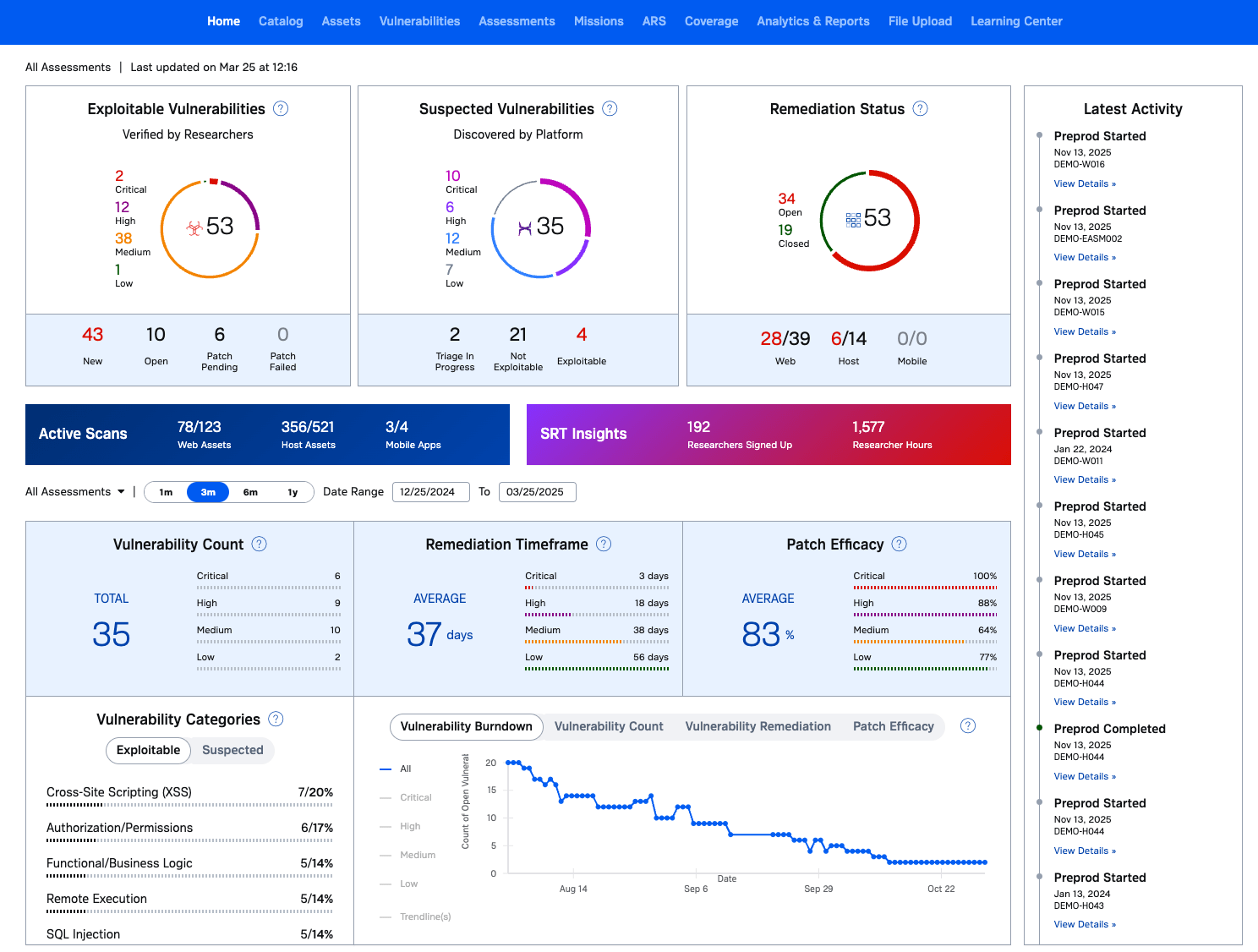
AI Pentesting for Continuous Security Validation. Test Your Entire Attack Surface. Validate Real Risk. AI finds more vulnerabilities. Human experts prove what actually matters.
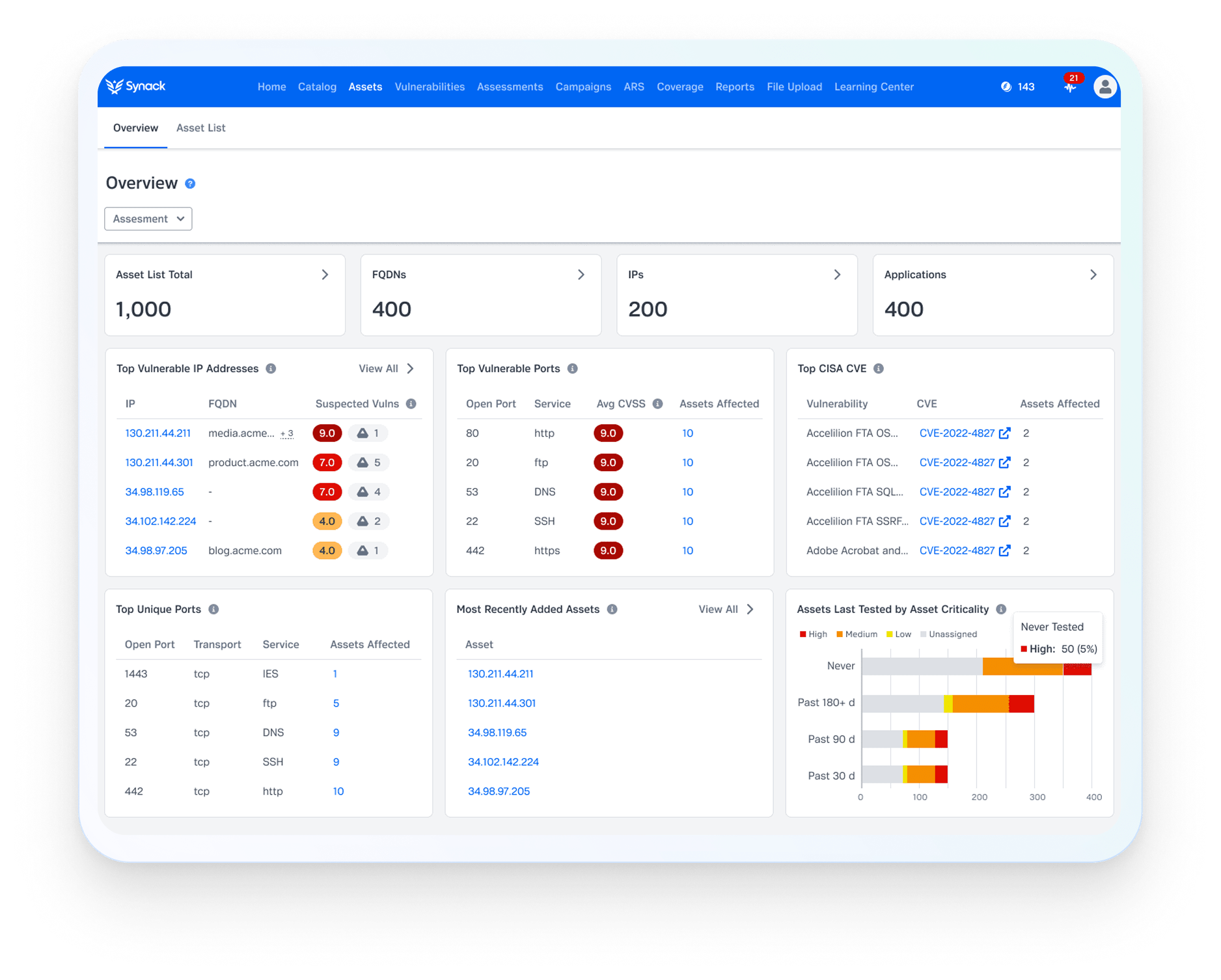
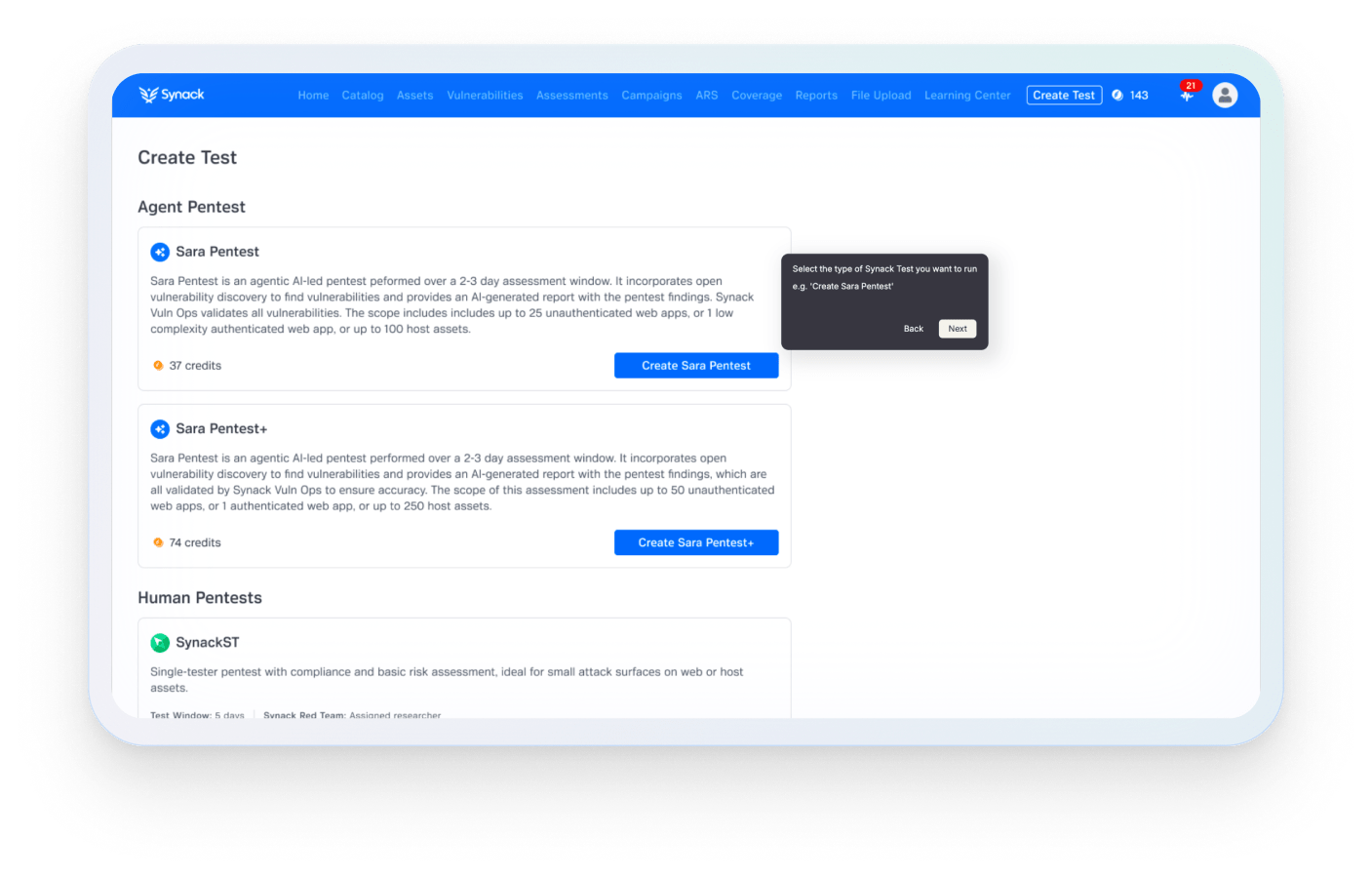
Most organizations test only a fraction of their attack surface. Sara AI Pentesting expands coverage across your environment, while the Synack Red Team validates real, exploitable risk. Together, they deliver continuous security validation—not periodic testing.