Splunk and Synack Partner to Bring Both a Defense and Offensive Strategy
In the cyber realm, organizations are often running their defensive and offensive security operations with little coordination. Defensive security techniques, such as firewalls, endpoint detection and response, network access control, intrusion prevention and security information event management, detect and stop attackers. While offensive security offers a way to test the effectiveness of cyber defenses. These […]

In the cyber realm, organizations are often running their defensive and offensive security operations with little coordination.
Defensive security techniques, such as firewalls, endpoint detection and response, network access control, intrusion prevention and security information event management, detect and stop attackers. While offensive security offers a way to test the effectiveness of cyber defenses. These include techniques and tools such as red teaming, penetration testing, vulnerability assessments and digital reconnaissance. Too often organizations focus on defensive security and not enough on offensive security testing.
Red Team vs. Blue Team
By design, security offense and defense teams work separately, with the red team or pentesters probing the attack surface looking for weaknesses, much like malicious hackers might. Without consistent and frequent communication between the two, the defense won’t know where to make improvements.
Security Operations Centers (SOC) focus on defensive cybersecurity. SOCs use many defensive security tools, as such they need a single pane of glass to view and correlate the data points coming from each source. Splunk Enterprise and Splunk Cloud (Splunk) are data platforms at the center of security operations that provide insights across disparate data streams to achieve end-to-end visibility for SOCs. Often missing are the results of offensive security testing into the SOC’s single pane of glass.
To combine offensive security data, Synack offers an add-on app for Splunk. This allows the SOC to view, correlate and receive alerts for the results of offensive security tests and recommended fixes to their defensive security in real time.
When information about security flaws isn’t accessible by the SOC, vulnerabilities and exploits uncovered by offensive security testing are reviewed only occasionally (e.g. in conjunction with periodic events such as yearly security compliance audits). New types of threats appear daily, so an occasional review isn’t sufficient to maintain good security posture. However, given the opportunity, Splunk’s architecture can ingest dynamic offensive security testing results and make such results actionable by security leaders.
An organization’s defenses can, and should, be tested against the latest security threats, not just the ones needed to pass a yearly compliance audit.
The Synack Integration with Splunk
Synack helps address these challenges by offering a premier security testing platform, supported by an expert, vetted community of security researchers who run continuous vulnerability assessments and deliver on-demand pentesting as new exploits emerge. The Synack Red Team (SRT)—1,500+ members strong—allows customers to take advantage of a diverse and instantly scalable security talent pool without the overhead of static headcount to accommodate surges in testing demand. Customers get offensive security testing 365 days a year with actionable reports to empower them to tackle new risks as they occur.
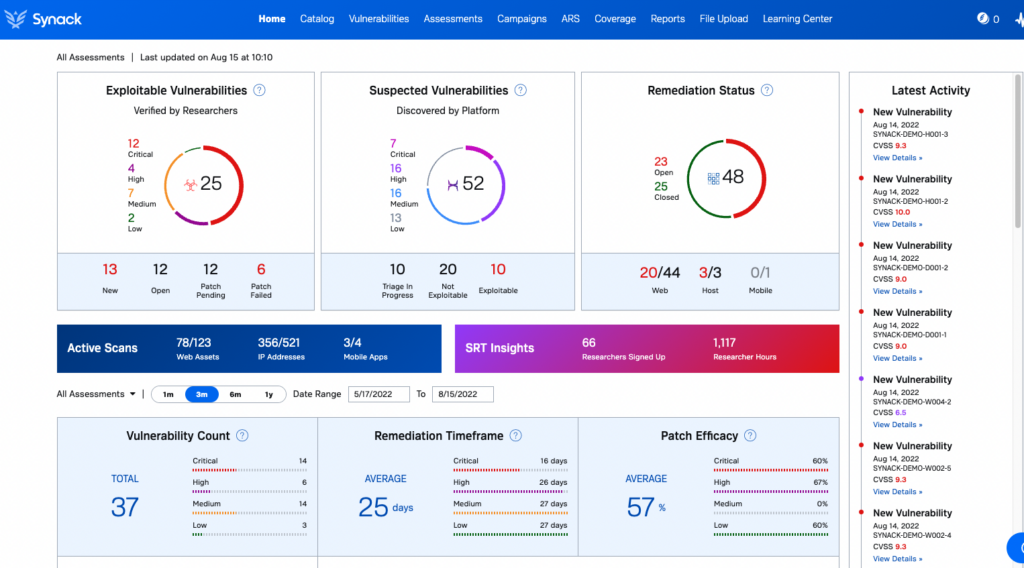
The Synack integration with Splunk uncovers exploitable vulnerabilities that can be correlated with network traffic, logs and other data collected by Splunk to recommend more effective security policies and rules on defensive tools (e.g. intrusion prevention systems and web application firewalls). Progress to harden an organization’s attack surface can be made by reviewing results, verifying recommendations and patching fixes (which can be verified by the SRT). The integration automates this process by facilitating continual improvement in security posture.
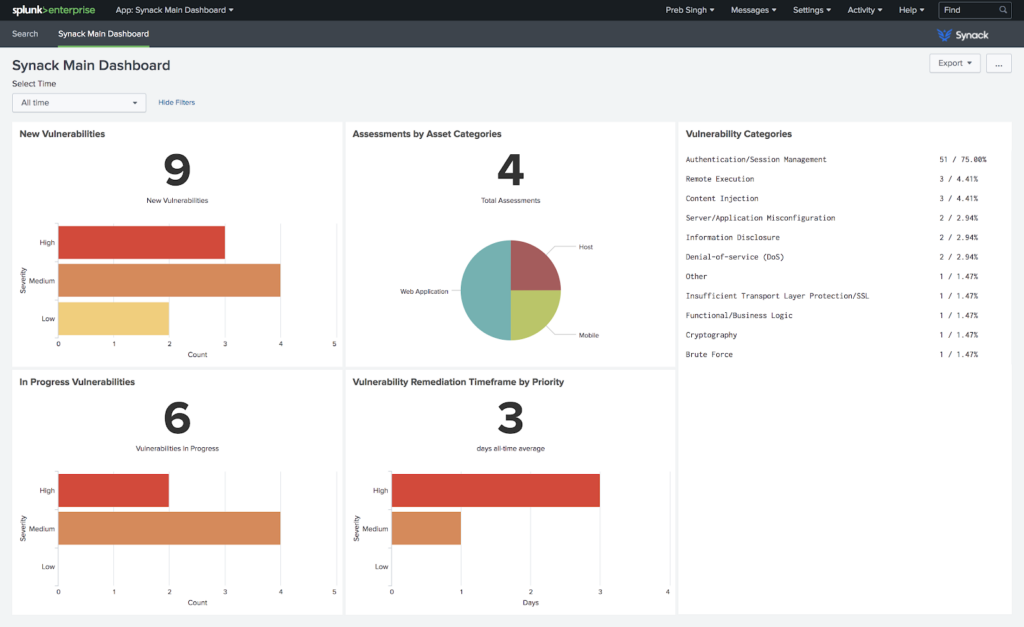
With the integration between Synack and Splunk, organizations can seamlessly coordinate offensive security into their SOC. This enables continuous defensive improvement in cyber security posture and protection. Splunk and Synack help all your team members work from the same playbook.
To learn more about Synack’s premier security testing please visit our website, to learn about Splunk see their site and to access the Synack Integration with Spunk please visit the Splunkbase.






